If human beings are the weakest link in cybersecurity, how much of that really comes down to social engineering and basic common sense? The most common types of security threats hitting businesses hard are ransomware, malvertising, and CFO fraud, and according to Chris Boyd, intelligence analyst at Malwarebytes, all three depend on exploiting basic human trust.
Malwarebytes analysed a cross section of systems protected in the UK, which revealed that workers in the City of London are the most susceptible to ransomware attacks. As a global finance hub, London’s square mile famously houses banks, law firms and corporate finance companies, which could explain why the City suffered 670 per cent more ransomware attacks than the next nearest hub, Manchester.
The data, compiled by Malwarebytes Data Science and Engineering team, analysed threat intelligence from a representative sample over the course of a little more than a year, breaking these down by location. In the sample set, the City of London had nearly 10,500 ransomware hits, more times than Sweden, Malaysia and Hungary.
The dataset also outlined the top ten pieces of ransomware attacking people in the UK., with File Cryptor, File Locker, Trojan Ransom, TeslaCrypt and Cryptowall leading the list.
The most common form of attack essentially demand money with menaces, encrypting company files unless a ransom is paid. “Workers in the city presumably have terrible social engineering and lack softer people skills,” Boyd explains. “A lot of the time, its an intertwined issue between IT and HR. It’s a little bit about using common sense, but it’s mostly the lack of training on the human side.”
Some of the tactics that scammers use are still pretty basic, according to Boyd, yet people fall for them time and again. “There’s no real incentive for companies to train employees (on how to identify fraud and avoid falling for scams).”
CFO fraud: Trust no one
Most scams work because they bank on victims trusting the system. Of Boyd’s top three security threats, CFO fraud may be the most insidious. It works on the legitimacy of your business, he tells GrowthBusiness. Scammers can look up your company and see all the registered entities and names associated with the business – usually finance personnel. “These scammers check out LinkedIn profiles and Twitter accounts of all the names they find. They figure out email formats in the company. It’s really simple for them to create a fake account that looks close to the real thing,” he says.
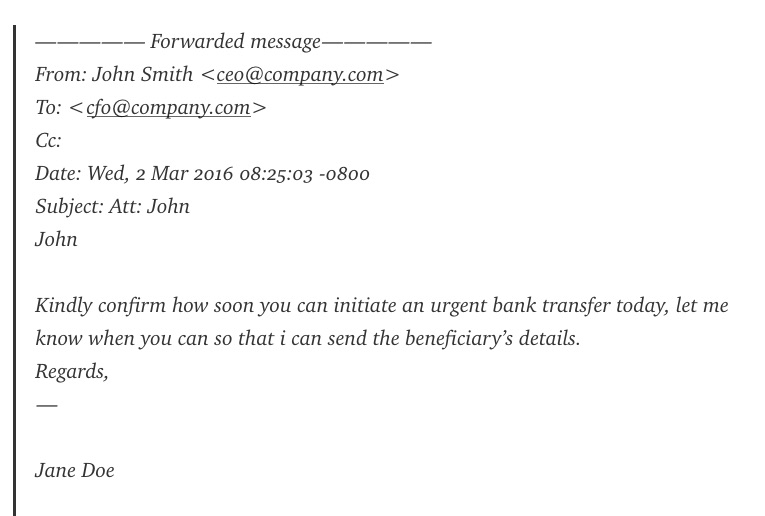
Most people only look at the first part of a url, and if that looks right, an extra vowel or switched letter won’t register. Scammers know this, and send fraud emails pretending to be the CFO of the business, in dire need of a quick money transfer. Scammers send between three and five “urgent” emails within the hour, which places an unnecessary time crunch on more junior staff. Victims of this type of fraud miss the red flags, and crumble when faced with the urgency of these emails and the fear of disappointing higher-ups.
In one case, a company lost $44 million. “It’s never a nice round number, either,” says Boyd. “Scammers know that in finance, invoices aren’t rounded up. They also carry out this fraud in small increments so banks aren’t alerted.”
There are tools to fake authentication at the bank level, and once the money is wired, it’s gone.
Malvertising: not only on nefarious sites
“There’s a general attitude towards victims of (fraud): ‘you clicked on something dodgy, serves you right.’ But it’s not just dodgy websites that can put you at risk. Rogue advertising is a very real thing,” Boyd says. These ads aggressively redirect users away, download malware on their devices that can run in the background. The worst part is that even respectable sites can host these kinds of ads, with campaigns starting out legitimately and “flipping the switch from good to evil” whenever they feel like, Boyd explains. “Webmasters simply cannot control affiliate accounts. And installing adblocker on each business device isn’t practical.”

Malwarebytes has worked with network admins to shut down malicious campaigns, but on the most part, when scammers see domains are protected with anti-exploit software, they are more likely to move along. “These scammers check to see if the person who’s clicked on their dodgy link are the type they want to infect. Seeing anti-exploit software on their system is a red flag for them.”
Scaremongering or basic hygiene?
The world of cybersecurity is rife with scary statistics, but ultimately, like with most things, Boyd believes that it comes down to common sense. “There’s a risk with everything being hijacked, stolen and so on. To some extent, people worry if having security tools could open them up to more threats. But at what point then does your computer become a useless box? I feel sorry for security people. If they play (threats) down, that’s a risk, but if they explain it in a sensational way, then it’s scaremongering. Information should be presented to different people in different ways.”
At a basic level, Boyd stresses that layering security, keeping security systems up to date, and stressing the importance of common sense in surfing the internet remain the best way to stay ahead of fraud.






